14 Recon Phases for Mastering Bug Bounty Hunting
Bug bounty hunting is a process of identifying and reporting vulnerabilities in a company's...

TryHackMe | Django: CVE-2025-64459 | WriteUp
Explore and learn about the Django CVE-2025-64459 vulnerability
One Random Recon, One Real Bounty
From countless dead ends to a single Swagger UI payload — the unexpected breakthrough that...

4 Deep Recon Techniques
⚠️ Note: This information is only meant for educational and ethical vulnerability research...
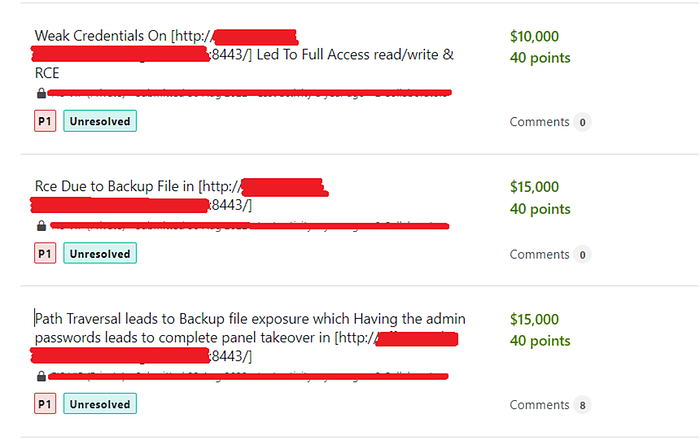
A Journey of Limited Path Traversal To RCE With $40,000 Bounty!
#Introduce Myself:

Bug Bounty Hunting 101: "Choosing the Perfect Target"
Are you tired of constantly coming up empty-handed in your bug bounty hunting endeavors? Are you...
The Bug Hunter's Guide to Privilege Escalation: 5 Real-World Examples and How to Leverage Them
As a bug hunter, discovering privilege escalation vulnerabilities is a valuable and lucrative...

The Top 10 Platforms Every Hunter Should Know
Are you tired of sifting through countless search results and unsure which websites truly have...

From $0 to Your First Bug Bounty: A Beginner's 14-Day Roadmap (2026, No Paid Tools)
What Bug Bounty Really Looks Like for Beginners in 2026

Blind XSS through PasteJacking: A Detailed Guide to Clipboard Exploitation
Discover how attackers abuse clipboard paste handling to trigger Blind XSS from setup to...
10 Java Basic Concepts Every Developer Should Know (Even Seniors Too)
"Java basics are not basic — they are fundamental."
How I Turned a Headless Browser into a Critical SSRF Goldmine
Three months. That's how long I stared at bug bounty programs, submitting low-risk findings...
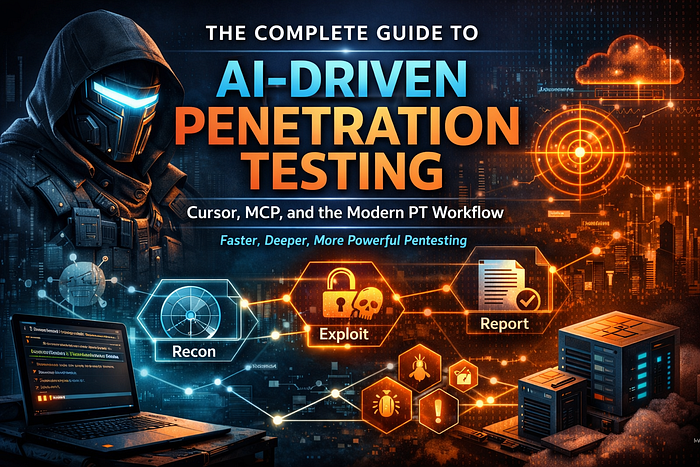
The Complete Guide to AI-Driven Penetration Testing: Cursor, MCP, and the Modern PT Workflow
A comprehensive, step-by-step guide to running penetration tests the way that actually works —...

CVE-2025-55182: A Pre-Authentication Remote Code Execution in Next.js - Complete Guide
Hey there, back again with another post! 😄

Open Redirect to XSS: Chaining Vulnerabilities for Maximum Impact
Hello guys! I'm back again with a real-life example of how I turned a simple open redirect...

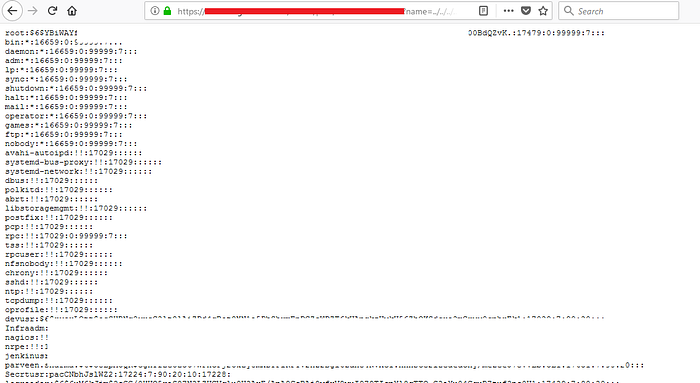
Exploiting Django CVE‑2025‑64459 on TryHackMe: Complete Walkthrough
How a tiny Django flaw turns simple filters into full‑database leaks.
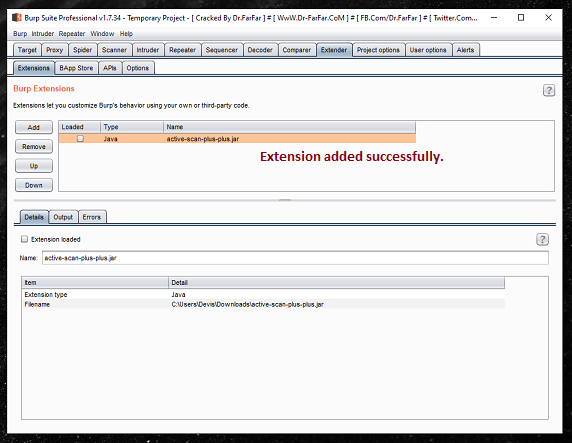
Burpsuite Extension: Active Scan++
What is Burpsuite Extension: Active Scan ++ ?
How to Use Better Translation Service on Immersive Translate for Free?
Use Immersive Translate Here:

5 Advanced Bug Hunting Techniques for Experts (Part -1)
Bug hunting is a critical part of ensuring the security and stability of software systems, and it...

Mastering Blind XSS: Real-World Techniques for High $Bounties
From simple dorks to advanced metadata injection, here's a complete walkthrough of the...

My 5-Minute Workflow to Find Bugs on Any Website
A step-by-step guide to my most effective, shortcut methods for bug bounty hunting.
Burp Suite Automation: 12 Custom Extensions That Save Hours for Pentesters and Bug Hunters
Ever spent hours manually fuzzing inputs or hunting for XSS, only to find out you missed a simple...
20 Cache Poisoning Case Study | Depth Analysis of Real-world Bug Reports
An in-depth analysis of real-world cache poisoning vulnerabilities discovered on major platforms,...

🔎 How to Read JavaScript Files for Hidden Endpoints

Bug Bounty Hunting: A Comprehensive Guide in English and french
· ~4 min read · March 7, 2026 (Updated: March 7, 2026) · Free: No🔎 One of the Most Powerful Recon Techniques in Bug Bounty
Hidden API Endpoints: The Hacker's Secret Weapon 🔍
I'm a cybersecurity enthusiast and the writer behind The Hacker's Log — where I break down...
Internal vs External Pentest: 12 Tools Clients Don't Know Exist (and How Pros Use Them)
Ever sat across from a client, nodding as they ask about "just running Nessus or nmap"...
Uncovering Hidden Gems: 5 Advanced Bug Hunting Techniques (Part-2)
Bug bounty hunting is a challenging and rewarding field, but it can also be a crowded and...

Actuator Unleashed: A Guide to Finding and Exploiting Spring Boot Actuator Endpoints
A hands-on walkthrough to find, test and exploit Actuator endpoints for bug hunters.
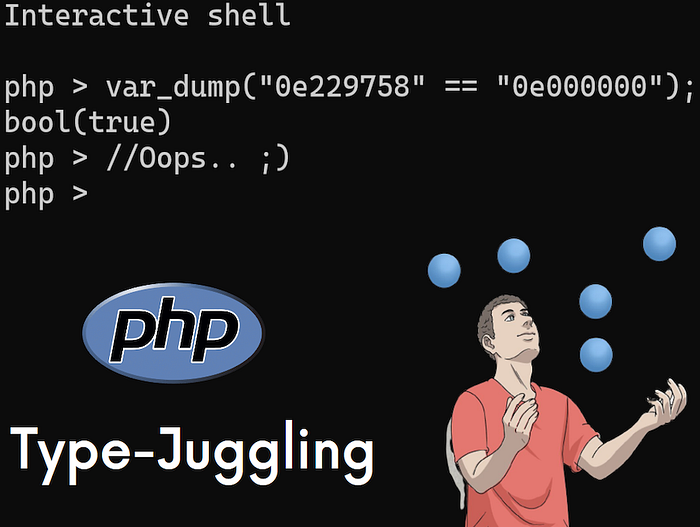
PHP Type Juggling Vulnerability
What is Type Juggling:

⚠️ Angular Signals in Production — What Broke After 3 Months (Real Lessons)
Three months ago, we migrated a major feature module to Angular Signals.
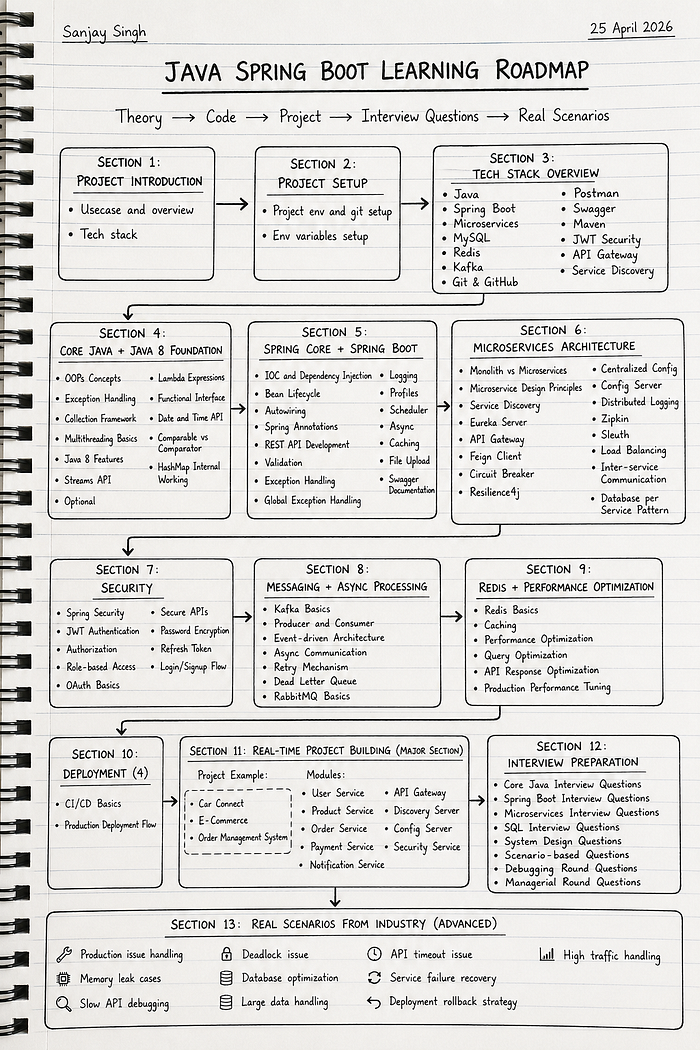
Java Spring Boot Microservices Learning Roadmap (2026)
Theory → Code → Project → Interview Questions → Real Scenarios

Web Shell Upload via Extension Blacklist Bypass — File Upload Vulnerability
In today's Pentesting Methodology Lab Walkthrough at the Cybersec Cafe, I'll be approaching...
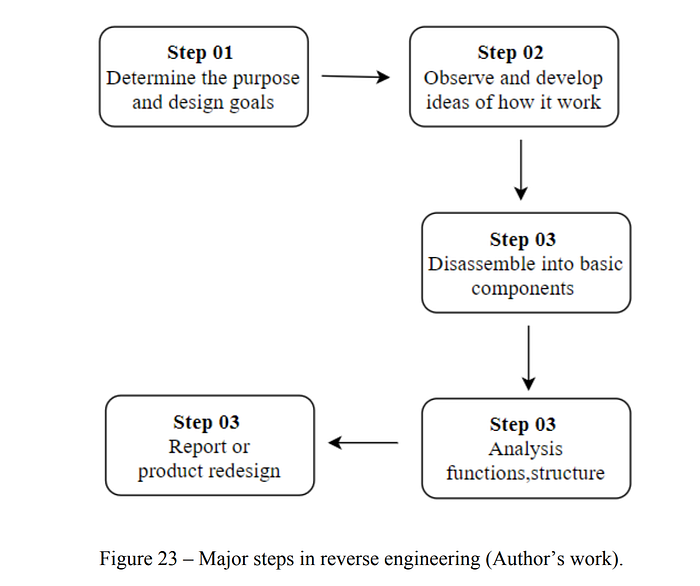
Primary Methods to Reverse Engineering PE Files (.exe Files)
Revere engineering, also called back engineering is the process by which a man-made object is...
Complete Guide to Dnsx for Mass DNS Resolution and Bug Bounty
Essential guide to mass DNS resolution, takeover detection, and sensitive records in bug bounty...

How I Found a $2,800 Bug in 60 minutes — and How You Can Spot It Too
The $2,800 Bug That Took Just 1 Hour to Find

🧰 My Bug Bounty Tool Stack (2026 Edition)

Bug Bounty Hunting: A Comprehensive Guide in English and french
· ~3 min read · February 12, 2026 (Updated: February 12, 2026) · Free: No🧰 My Bug Bounty Tool Stack (2026 Edition)
Cursor AI's Leaked Prompt: 7 Prompt Engineering Tricks for Vibe Coders
Advanced Prompt Engineering Techniques From Cursor's System Prompt

Mastering SQLMap and Ghauri: A Practical Guide to WAF Bypass Techniques
Step-by-Step Methods to Identify, Exploit and Bypass WAF Protections

🔍 Power of One-Liners: Master Bug Bounty Automation: 🔍
🚀 Supercharge Your Bug Hunting with Brilliant One-Liners and Crush Vulnerabilities! 🚀

Top 25 Race Condition Bug Bounty Reports
In this article, we will discuss Race Condition vulnerability, how to find one, and present 25...

🚀 From Zero to $100K: How to Become an AI Hacker in 6 Months (While Everyone Else Missed the Boat)
You type a simple message into ChatGPT, and suddenly it spills its entire system prompt, reveals...