⚠️ Note: This information is only meant for educational and ethical vulnerability research purposes. Author not responsible for any actions! You are advised to ethically report any vulnerability found to it's respective BBP/VDP Program.
1️⃣ Unique Phrase Recon leading to targeted subdomains
"You are accessing a" site:nasa.gov
"Employee Login" site:nasa.gov
"Employee" "Forgot password" site:nasa.gov
inurl:servlet/sm.web.Fetch site:nasa.gov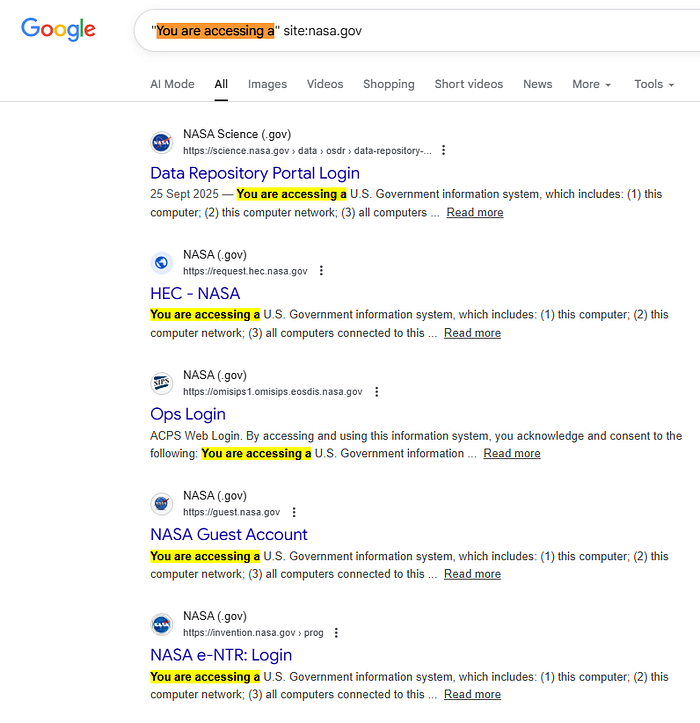
Sort by latest for newly indexed results.
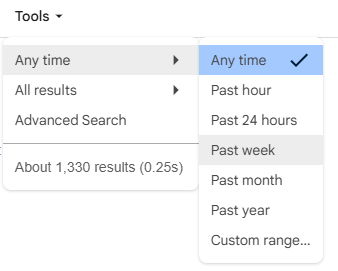
2️⃣ Parameter Hunt via FOFA Dorking
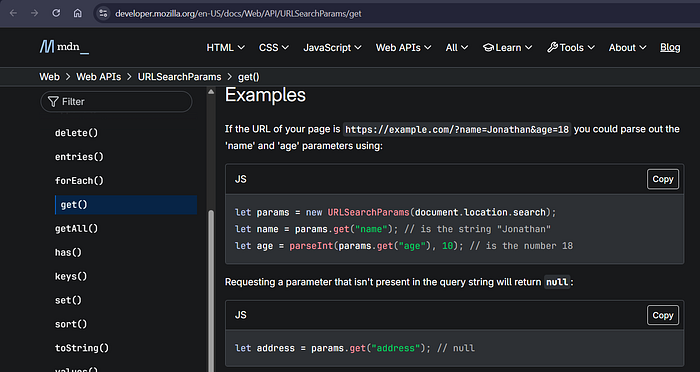
domain="example.com" && body="new URLSearchParams"
domain="example.com" && body="params.get"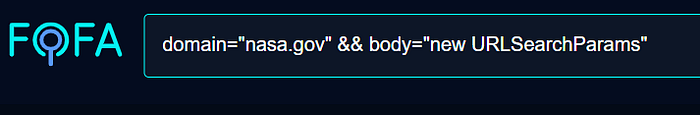
Quick Reference for beginners
3️⃣ API Documentation Hunting
site:nasa.gov "Swagger UI"
site:nasa.gov "JSON REST API"
site:nasa.gov "DELETE /" "/users" "PATCH /"
Some endpoints won't be documented, but it leads to PII leak.
Example directly visiting endpoint like /users , /allusers , /all_users
Sometimes you need not fuzz, it can be a guesswork as well 🤘
4️⃣ Github Source Code Recon
org:example "@app.route"
org:example "@app.get("
org:example "@app.post("
org:example "router.get("
org:example "router.post("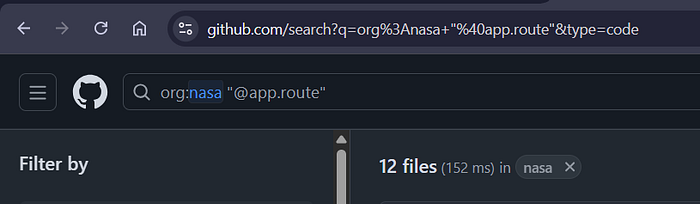
Find old API version
org:example "/api/" "/v1/"
org:example "/api/" "/v2/"Admin Endpoints
org:example "/api/" "/admin/"
Websockets
org:example "new WebSocket("Issues Hunt (Goldmine 😈)

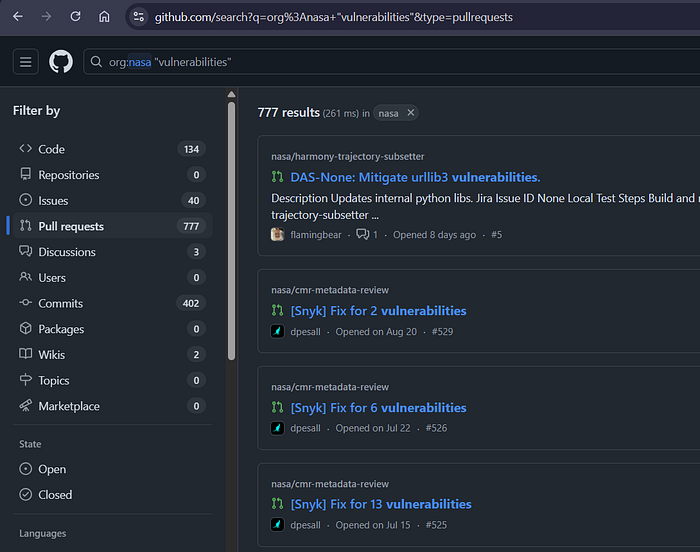
Pull Requests
This is not directly related to this target, but in general tips & tricks.
First learn secure coding in various programming languages, then make a dictionary of patterns/ keyword that you can mass hunt everywhere.
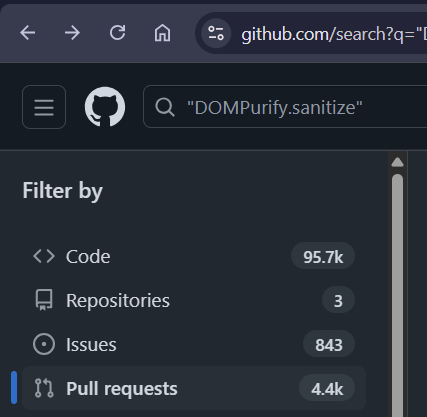
Always ask 3 things
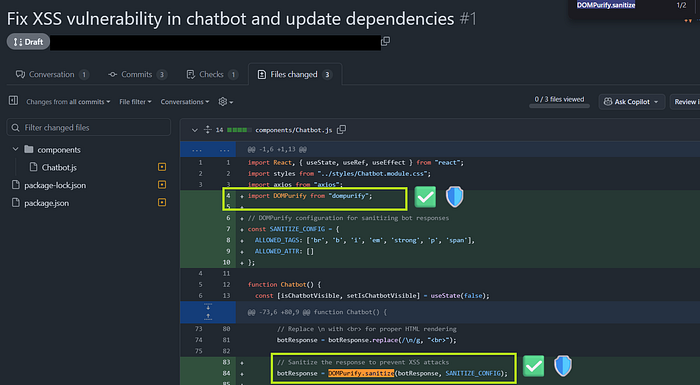
- What was the vulnerability reported ?
- How the developer patched the vulnerability ?
- Okay, now can we bypass it?
Hunting Niche: Bypassing already fixed vulnerabilities (fixed insecurely)
How it is possible to bypass ?
Even if the developer uses the strongest library / framework, they need to implement it the right way to prevent all edge case scenarios. Half knowledge is dangerous :)
That's the end for today! Want more deep recon techniques ? Check below 😎
Make sure you are enjoying the stuff to auto-unlock new potential 🤘



